protect-pointcut in Spring Security
November 27, 2019
Spring Security provides protect-pointcut to handle security in service layer of application. All methods of more than one class can be secured just by matching a pattern. In this way by small code, we secure many classes in one go. In our example we will see the entire required configuration to add security pointcuts using protect-pointcut within global-method-security namespace in Spring Security XML file. The global-method-security namespace is used for security configuration. Find the code to use protect-pointcut.
<global-method-security >
<protect-pointcut expression="execution(* com.concretepage.service.*Service.*(..))"
access="ROLE_USER"/>
</global-method-security>
com.concretepage.service can be access only with ROLE_USER. Now find the complete demo.
We have a service class and its interface as below.
ILoginService.java
package com.concretepage.service;
public interface ILoginService {
public String welcome();
}
package com.concretepage.service;
public class LoginService implements ILoginService {
public String welcome(){
return "You are authorized for this zone.";
}
}
LoginController.java
package com.concretepage.security.controller;
import java.util.Collection;
import javax.servlet.http.HttpServletRequest;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.security.core.GrantedAuthority;
import org.springframework.security.core.context.SecurityContextHolder;
import org.springframework.stereotype.Controller;
import org.springframework.ui.ModelMap;
import org.springframework.web.bind.annotation.RequestMapping;
import org.springframework.web.bind.annotation.RequestMethod;
import com.concretepage.service.ILoginService;
@Controller
@RequestMapping("/login")
public class LoginController {
@Autowired
public ILoginService loginService;
@RequestMapping(method = RequestMethod.GET)
public String success(ModelMap map,HttpServletRequest req) {
if(hasRole("ROLE_USER")){
String msg = loginService.welcome();
map.addAttribute("msg", msg);
}else{
map.addAttribute("msg", "Successfully logged in but You are not authorized for this zone.");
}
return "success";
}
private boolean hasRole(String role) {
Collection<GrantedAuthority> authorities = (Collection<GrantedAuthority>)SecurityContextHolder.getContext().getAuthentication().getAuthorities();
boolean hasRole = false;
for (GrantedAuthority authority : authorities) {
hasRole = authority.getAuthority().equals(role);
if (hasRole) {
break;
}
}
return hasRole;
}
}
security-config.xml
<?xml version="1.0" encoding="UTF-8"?>
<beans:beans xmlns="http://www.springframework.org/schema/security"
xmlns:beans="http://www.springframework.org/schema/beans"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://www.springframework.org/schema/beans
http://www.springframework.org/schema/beans/spring-beans-3.0.xsd
http://www.springframework.org/schema/security
http://www.springframework.org/schema/security/spring-security-3.1.xsd">
<http auto-config="true">
<intercept-url pattern="/login" access="ROLE_USER,ROLE_SUPERWISER" />
<logout logout-success-url="/login" />
</http>
<authentication-manager>
<authentication-provider>
<password-encoder hash="sha"/>
<user-service>
<user name="ram" password="0733824cc1549ce36139e8c790a9344d1e385cd2" authorities="ROLE_USER" />
<user name="shyam" password="0733824cc1549ce36139e8c790a9344d1e385cd2" authorities="ROLE_SUPERWISER" />
</user-service>
</authentication-provider>
</authentication-manager>
<beans:bean name="loginService" class="com.concretepage.service.LoginService"/>
<global-method-security >
<protect-pointcut expression="execution(* com.concretepage.service.*Service.*(..))"
access="ROLE_USER"/>
</global-method-security>
</beans:beans>
Output

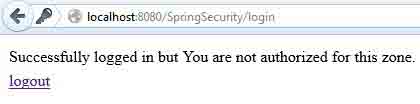
When we enter username ram and password con1234, we will see the below UI.
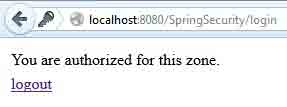
When we enter username shyam and password con1234, we will see the below UI.